Reconstructing User Activities from a Memory Dump
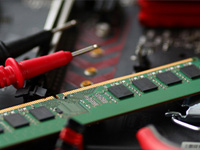
This training is intended for U.S. Criminal Justice Practitioners. Please register using your agency-issued email. Child exploitation cases often involve analyzing digital device storage drives to reconstruct user activities. While much can be learned from disk analysis, Random Access Memory (RAM) is a particularly rich source of potential evidence related to user activities. Specifically, reconstruction … Continue reading Reconstructing User Activities from a Memory Dump